In this age of technology the increasing presence of cyber threats poses a danger to individuals and their digital possessions. Whether its information, financial data or confidential documents the need, for cybersecurity measures has never been more crucial. It is vital to implement strategies to defend yourself against cyber attacks and protect your presence.
Here are some important tactics to bolster your digital defenses:
Creating Strong Passwords and Authentication
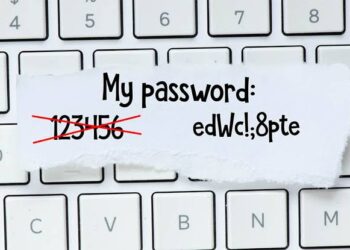
The first and fundamental line of defense against cyber threats involves the establishment of robust passwords. It is important to create passwords that encompass a combination of letters, numbers, and symbols to enhance complexity.
Additionally, it is important to enable Multi-factor authentication (MFA) for added security. MFA introduces an extra layer to the login process, necessitating users to verify their identity through multiple authentication methods, thereby fortifying access control.
Regular Software Updates

Regularly updating your software is a crucial proactive measure in cybersecurity. It serves as a defense against evolving cyber threats by closing vulnerabilities in your operating system, antivirus software, and applications.
This process enhances your digital defenses by deploying the latest security patches to address known vulnerabilities before cybercriminals can exploit them.
Operating system updates improve stability and functionality, while antivirus software updates empower it to recognize and neutralize emerging threats. Application updates not only enhance security but also provide access to the latest features.
You should also incorporate scheduled checks for software updates into your routine. Regularly review and ensure that your devices are configured to check for updates at specified intervals
Regular Backups

A good backup strategy functions as a safety net against cyber threats, ensuring the recovery and restoration of vital data in the face of loss, system failures, or ransomware attacks. This proactive measure mitigates potential disruptions to both business and personal activities.
You can enhance your backup strategy by diversifying storage locations.
You should explore secure cloud services alongside traditional external hard drives. This multi-location approach minimizes the risk of losing critical data, providing added resilience in case of a compromise to one storage medium.
It also ensures the availability of your files even if your device is compromised, eliminating the need to succumb to ransom demands. Regular backups are a cornerstone of effective data recovery.
Limit Personal Information Sharing

Limiting personal information sharing is a fundamental practice in safeguarding yourself against potential cyber threats. You should exercise caution, particularly on social media platforms, where oversharing can make you susceptible to targeted attacks by hackers. You can minimize the data available for exploitation by reducing the amount of personal information you disclose on the internet.
You can also take further steps to enhance your control over this information by adjusting privacy settings on your social accounts. These settings allow you to restrict access to personal details, ensuring that only authorized individuals can view specific aspects of your profile.
This approach to managing your online presence contributes significantly to your overall digital security.
Avoid clicking unverified links

Another way to safeguard yourself against cyber threats is to avoid clicking unverified links. This involves exercising caution when encountering suspicious communications, verifying the legitimacy of senders, staying aware of phishing tactics, and refraining from financial transactions through unverified links.
Cybercriminals frequently employ tactics such as sending emails or messages in order to deceive individuals into divulging information. Therefore you must be cautious to significantly reduce the risk of falling victim to deceptive tactics employed by cybercriminals, particularly in phishing attacks.
In Conclusion, as our dependence on digital platforms deepens, prioritizing cybersecurity measures has become paramount. By diligently following these strategies, individuals can significantly strengthen their defenses against cyber threats and safeguard themselves online.
Remember, staying vigilant and proactive in cybersecurity is the key to maintaining a secure online presence in an increasingly interconnected world.






